Table of Contents
“Dear Sir or Madam,“—Ouch. A cybersecurity cover letter like this will be treated like the Nigerian prince scam. To get an information security job at Protonmail or Symantec, you need a cover letter that will work like a catfish.
Here’s a pentested formula.
This guide will show you:
- A cyber security cover letter sample better than 9 out of 10 others.
- The work plan for how to write a cover letter for information security.
- Tips for entry-level cybersecurity cover letter that will get you ahead of the race.
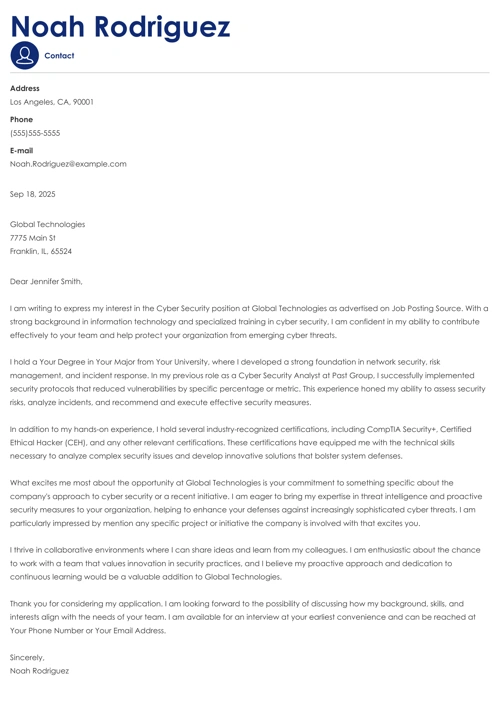
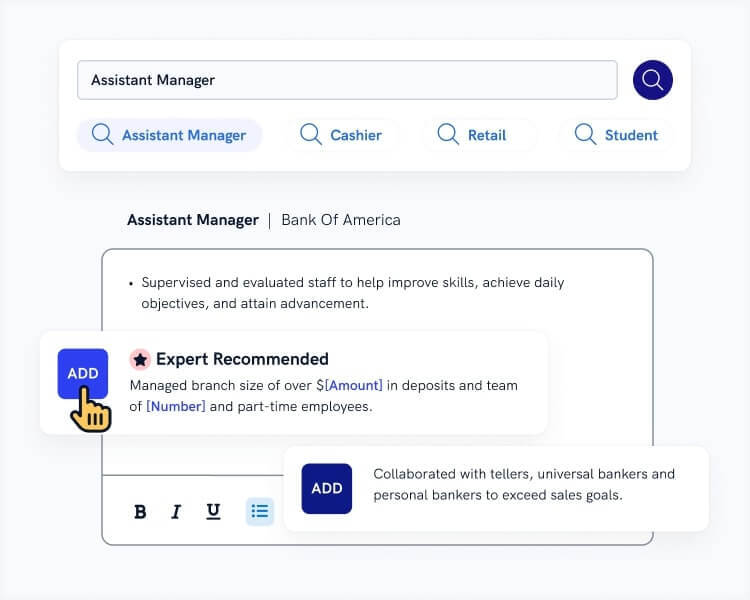
Want to write your cover letter fast? Use our cover letter builder. Choose from 20+ professional cover letter templates that match your resume. See actionable examples and get expert tips along the way.
Cybersecurity Cover Letter for a Resume—See more cover letter templates and create your cover letter here.
One of our users, Mikhaela, had this to say:
I am putting 100% trust in Zety for my resumes and cover letters because everything has become so simple with them. From their detailed explanation of almost everything to their great tips per section!
Perhaps you wish to read more than a cover letter for cyber security? See other guides we wrote:
- Business Analyst Cover Letter Example
- Computer Science (CS) Cover Letter Example
- CIA Cover Letter Example
- Data Analyst Cover Letter Example
- Data Scientist Cover Letter Example
- Front-End Developer Cover Letter Example
- Federal Cover Letter Example
- IT Cover Letter Example
- IT Technician Cover Letter Example
- Software Engineer Cover Letter Example
- Web Developer Cover Letter Example
- Entry-Level Cover Letter Example
- Best Cover Letter Examples For All Jobs
Cyber Security Cover Letter Example
Richard T. Hahne
Cyber Security Specialist
4364 Forest Drive
Falls Church, VA 22042
703-849-6106
richhahne@email.com
linkedin.com/in/richardrhahne
Falls Church, 5/31/2021
Vincent L. Locklin
Head of Information Systems
Cyber O’Clock Inc.
310 Broadcast Drive
Beltsville, VA 20705
Dear Vincent,
Throughout the years, I have been carefully observing your company’s drive for fulfilling your vision because I am, too, a passionate believer in integrating network and security infrastructure. Thanks to following your company’s blog advice, I stayed on top of information security and produced impressive outcomes as a network engineer at HWE Inc. Now I am after a cyber security specialist position at Cyber O’Clock Inc. to use my expertise to create a working environment that’s free of cyber threats.
From the moment my interest in cyber security spurred, I have become a Certified Information Systems Security Professional (CISSP) and CompTIA Advanced Security Practitioner (CASP+). You will also be keen to know that I obtained Top Secret security clearance with sensitive compartmented information (SCI) in 2018. My proudest moments at HWE Inc. to date are:
- Identification of over 300 new malware during 3-year work experience.
- Out-of-scope server monitoring for breaches and violations with ~4 major technical issues escalations.
- Conducting over 50 penetration tests to spot vulnerabilities, assess resource performance and allocation, and design disaster recovery plans.
Cyber O’Clock Inc. is a renowned cyber security company that guards data of such applications as Musify and B2Bair. You have experienced no breaches whatsoever, and as a regular user of the above services, I will make every effort to maintain a clean record.
Shall we schedule a meeting next week to discuss my value to your department?
With kind regards,
Richard T. Hahne
A solid backup plan means everything at your cyber security jobs, also when you’re trying to get one. The information security cover letter is just the support your need. So, before hitting send, do the penetration testing on this guide: Cyber Security Resume
Now let us deliver on the promise.
Information Security Cover Letter Template
Here’s the work plan for how to write a jaw-dropping IT security cover letter:
1. Set Up a Stable Cybersecurity Cover Letter Format
Without a stable network and security architecture, you won’t be able to perform. The same goes for your IT security cover letter.
Establish solid grounds when formatting your cover letter, and don’t let anything and anyone make threats to your product.
- Find a modern cover letter template that meets the environment requirements.
- Use proper cover letter spacing: 1-inch margins on each side, 1-1.5 line spacing, and double space between paragraphs.
- Choose the best business-like cover letter font in 12pt size.
- Left-align your letter. Don’t make your hiring manager jump from one word to another because ofyour oops.
- Divide your cover letter structure into clear sections: header, introduction, body, closing, and signature.
- Title your cover letter file with your name and the position you’re applying for. See an example: Richard-Hahne_Cover-Letter_Cyber-Security-Specialist.
Read more: How To Write A Cover Letter For A Job Today
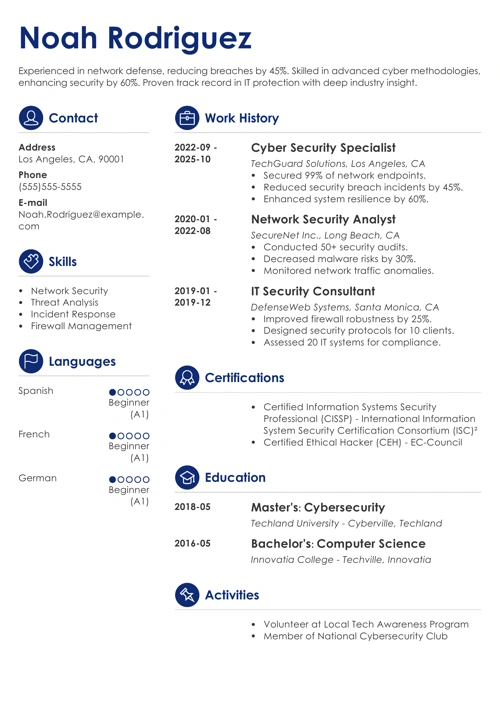
2. Link Your Information Security Cover Letter Header Design to Your Resume
Going through SOPs with no idea where you at?
Yeah. Happens to all of us. But—
It can’t happen to your hiring manager. They need to know who you are and what you want from the start.
- Duplicate the resume design in your cover letter for cyber security. Consistency looks good on you.
- Give your contact information: full name, mailing address, phone number, and email address.
- Mention your current title or the job you’re interested in.
- Add your social media links. Remember to optimize your LinkedIn account to stay professional.
- Mention the place and date of writing.
- Find your hiring manager details and address them. Make an effort to learn their name. If you can’t find it in all over the web, go ahead and call the reception.
- Salute with Dear [Hiring Manager’s name] in the cover letter. Don’t think for a second that To Whom It May Concern will break the firewall.
Read more: The Way To Address A Cover Letter
3. Identify and Apply the Best Fix to Your First Paragraph
Once upon a time, your password was admin.
But you aren’t a newb anymore, so generic cover letters and passwords are a flat-out no-go.
You won’t let your hiring manager press reset and move on to another application just because you lack imagination, will you?
- Use one of several strategies of how to start a cover letter. You can make an offer, a promise, drop names, or use one of your biggest achievements.
- Tailor your information security cover letter from the start by using resume keywords that you find in the job posting.
- Open strong. Don’t be afraid of action verbs and adjectives that describe your personality and abilities. Just be sure you’ll be able to prove what you wrote.
- Let them know you’re interested in joining the company, but be confident about your fit. You need to intrigue the hiring manager to make them go next to the cover letter body.
Read more: What Does And Does Not Your Cover Letter Say
4. Validate Your Qualifications and Skills in the Body of Your IT Security Cover Letter
So—
You’re waiting for the beat to drop. And, out of nowhere, your antivirus software sends you this blaring, earsplitting, and deafening sound followed by “The database has been updated.”
Jeez. I almost jumped out of my skin!
Your recruiter wants to be surprised, too. So, exceed their expectations with your achievements, rather than giving them a panic attack with a lack of problem-solving skills.
- The second paragraph of your cover letter outline is all about relevant experience and skills. Keep the attention you grabbed in the intro by proving you’ve got what they need.
- A list of responsibilities interests no one. Mention real-life examples with an in-depth description of your relevant qualifications and achievements at work.
- Quantify your achievements, use power phrases, and show your impact on the company’s development.
- In an entry-level cyber security cover letter, this is the moment you can elaborate on the relevant coursework you had in school or the internship you did. Boast about any transferable skills you picked up.
- Refer to the hard and soft skills mentioned in the job ad, yet avoid creating a never-ending list. Use power bullet points to pinpoint the requirements.
Read more: Elements Of An Exceptional Cover Letter
5. Re-Enter Your Reasons Why You Want the Information Security Job
Imagine you’re Elliot sitting on an empty subway and a shady Mr. Robot approaches you asking to follow him.
Whoa, buddy!
You know why you do the things you do, but working with a group of hackers?
FSociety or not, display your motivation to join their ranks in the last but not least paragraph.
- No matter if applying for a chief information security officer or an entry-level position, show your enthusiasm and excitement about joining the company.
- Tell the hiring manager why you want to join and prove you know what the company’s all about.
- Refer to the company’s mission, vision, and value statements.
- Give a specific example of a recent activity taken by the company and tell why they impressed you.
- Personalize this section because, after all, you’re not a robot.
6. Call to Action and Sign Off
You open strong, so the finish line can’t be any different. Write an impressive one-punch-line that Stieg Larsson would want in his Millennium series.
- Ask the hiring manager to schedule a call or a meeting to further discuss your application further. You don’t ask, you don’t get it.
- Sign off with a professional and respectful sentiment like With kind regards, Sincerely, or Best regards followed by your full name.
- (Optional) If you have one more ace up your sleeve, include a postscript in the cover letter closing. But it needs to add value like 0 to 1 in the binary code.
- Create a cover letter enclosure if you’re attaching a resume and other documents.
Read more: Ways To End A Cover Letter
Creating a resume with our builder is incredibly simple. Choose a resume template and follow our step-by-step guidance to have a professional resume ready in minutes.
When you’re done, our online resume builder will score your resume and our ATS resume checker will tell you exactly how to make it better.
And—
That’s it! You’re off to a great start as an information security professional.
Thank you for reading!
About Zety’s Editorial Process
This article has been reviewed by our editorial team to make sure it follows Zety’s editorial guidelines. We’re committed to sharing our expertise and giving you trustworthy career advice tailored to your needs. High-quality content is what brings over 40 million readers to our site every year. But we don’t stop there. Our team conducts original research to understand the job market better, and we pride ourselves on being quoted by top universities and prime media outlets from around the world.